- All-in-one
- 1 x Core i5 3.1 GHz
- RAM 8 GB
- Hybrid Drive 1 TB
- Radeon Pro 575X
- GigE
- 1 TB
- hot-swap
- 2.5" SFF
- SAS 12Gb/s
- 7200 rpm
- with HP SmartDrive carrier
- Solid state drive
- encrypted
- 500 GB
- internal
- M.2 2280
- PCI Express 3.0 x4 (NVMe)

Your IT environment is only as secure as your endpoints. iFix’s system engineers and security architects make it easy to secure all of your endpoints by offering recommendations and expertise on industry-leading solutions, including:


Our in-house solution architects provide guidance and pre-sales engineering services for your firewalls, email and web gateways, IPS/IDS, MFA, SIEM and more.

We help you establish criteria for network security success, create an ideal technical design and acquire demo products from OEMs. And better yet, our Customer Innovation Center lets you test your tech – before you buy.

We’ve got your back during every step of your implementation. We assist with configuration, delivery and health checks for all leading network security manufacturers.

We have what it takes to keep your network security project on course, from start to finish.
Need a hand? We’ve got project managers, network engineers and more to help you – whether you need them on a contract, contract-to-perm or permanent basis.
Does the phrase “out with the old, in with the new” apply to you? Our Asset Recovery Services have you covered when it comes to discarding old equipment.
Transparent: Stay informed at all times with our project timelines, thorough deployment coordination and more.
Efficient: We help you secure your network in a timely fashion, meaning you can save time, reduce costs and improve productivity.

Examine your security controls and processes from a holistic viewpoint to identify possible areas of improvement.
Test your staff through a variety of social engineering activities, including phishing, pre-texting and physical security evaluation.

Review existing internal and external perimeters to identify any rogue points of entry.
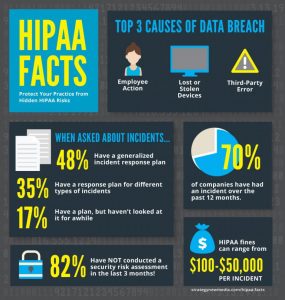
Stay compliant by comparing your current alignment with the latest HIPAA requirements.
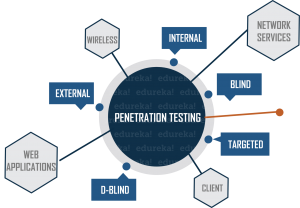
Simulate an attack on your system in order to determine where threats could sneak in and how to prevent them.